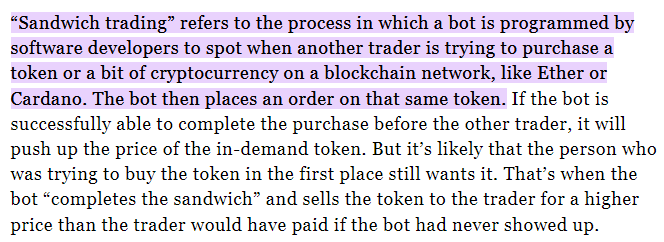
One of the most common arbitrage method is the sandwich bots or frontrunning bots where they front-run and back-run non stop.
Not exactly illegal but yeah, this is super common on Uniswap, PancakeSwap, Sushiswap and many others. They siphon the liquidity slowly.
- I guess some will argue that it actually makes the market more efficient.
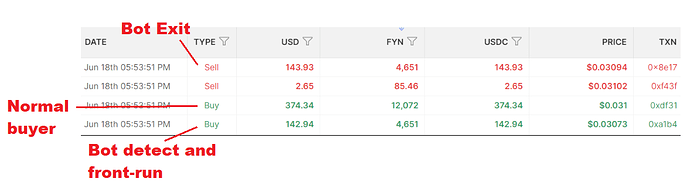
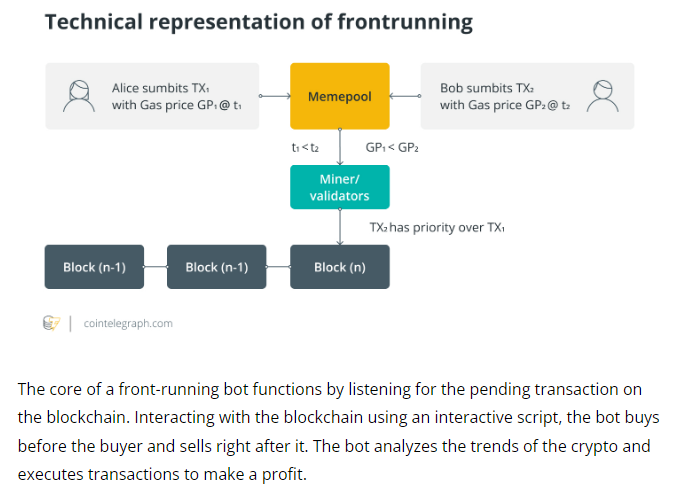
If the bot notices someone is trying to purchase a token in the mempool, the bot will front-run and purchase the token first at a cheaper price. Once the buyer buys it, the bot will then exit the position at a profit.
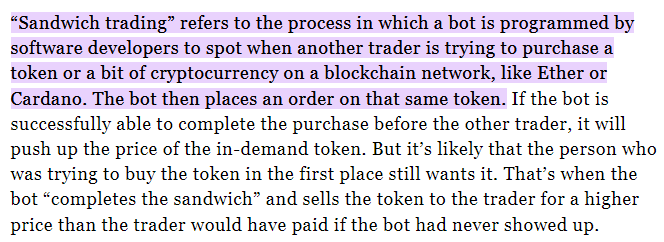
- Normal User places a buy order of token A
- Bot sees this in the mempool and front-runs it, pushing the price up
- Causes high slippage and the user gets a worse fill
- Bot back-runs user, selling back tokens at a higher price at a profit
In actual scenario, it looks like a simple buy and sell order from the same wallet.
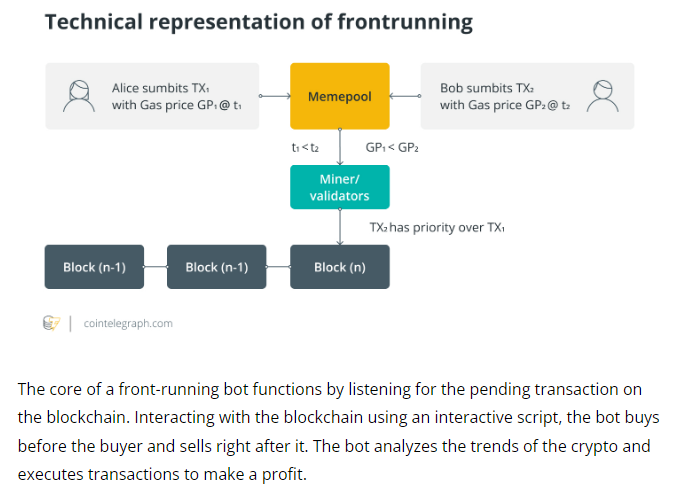
- They can also manipulate gas price & timestamps to frontrun for slow-matching dexes.
They don’t need to target large value transaction, it can also be done with small/mid value.
Enable “Limit Order” on FXSwap, this is what PancakeSwap did.
Not exactly a solution to the bots but this give users an extra layer of protection if they can buy/sell using limit order. With this, bots will have a harder time targeting people who just market swap.
PSC implemented a chart + limit order so the average user know what is going on in real-time at all times.
I private messaged you already, Dexter.
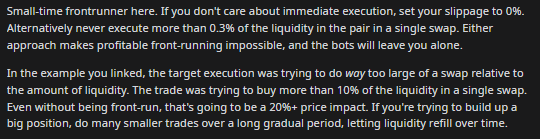
- There is no 1 solution that can fix this but one of the MOST important thing is to have a large liquidity pool.
Suggestion:
- I would suggest opening the liquidity provider pool first before the swap so the foundation and community members can help by providing enough liquidity to the pool first.
Just like how some exchanges open deposits first and wait till there is enough liquidity in the system before they open the trading for the new pair.
The method is designed to make frontrunning “harder” to execute, not totally prevent it from happening.
Frontrunners LOVE low liquidity pool because they can take advantage of the pool weight.
- Periodic auction matching
- Keep slippage as low as possible
- Frontrunners love slow transactions and they will always overpay gas fee to go first
- Quick matching - Fast block time will make most (not all) frontrunners not able to react
I think there are some more but i think too many to type here.
Not sure if this article will be of any help but some devs are trying to build something to protect users against bots. Maybe you will be able to find some ideas here.
- Another method is triangular bots i guess
https://blog.coinbase.com/quantitative-crypto-insight-an-analysis-of-triangular-arbitrage-transactions-in-uniswap-v2-1b572284bfa8